Tags are an incredibly useful yet often overlooked feature of most cloud computing platforms. Once created they let you manage your infrastructure more effectively by providing the ability to filter resources and perform tasks and actions based on nominated tag values.
Tags are essentially pairs of user defined metadata made up of a name and a value that are added to resources when they are created.
| Tag Name |
Tag Value |
| environment |
development |
| team |
security |
| department |
devops |
| status |
production |
In
AWS and
Azure these are referred to as "Tags" whereas
GCP refers to these as "Labels" apart from some network components where they are referenced as "Network Tags".
The rules related to tags do differ between platforms so some thought needs to be put into the naming conventions, especially if working with hybrid networks where you may want to construct documentation based on tag names and values.
| Platform |
Max Tag Length |
Max Value Length |
Allowed Chars |
Case Sensitive |
| AWS |
128 |
256 |
a-z, 0-9, + - =._:/@ |
Yes |
| GCP |
63 |
63 |
a-z, 0-9, _, - |
Yes |
| Azure |
512 |
256 |
a-z, 0-9, _, - |
No |
Tag names can be pretty much anything although the "aws:" tag is reserved within the AWS ecosystem.
Some platforms only allow lower case characters in tag names, so should you be planning or leveraging hybrid cloud architecture, then keeping to a naming convention that works across platforms is advisable.
One of the most common uses for tagging is to segregate billing information so you are able to report on network costs and usage for individual business units within your organisation or to perform automation processes on groups of resources with the same tag.
Tag Usage:
Console Organisation.
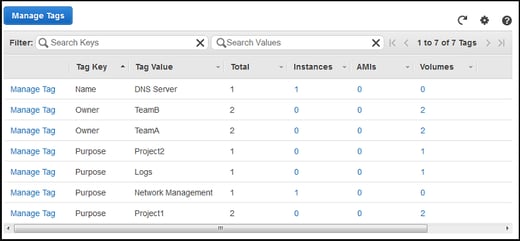
Filtering by tag is a quick way to narrow down the resources you are looking for in your console. Some platforms also allow you to create custom consoles based on partial or one or more tags
Cost Allocation.
Cost and usage reports generally support the ability to break down costs by tag. This enables cloud clients to report on costs for different projects or departments that share a cloud account. This is particularly useful for managed service providers to monitor the usage of multiple clients on the same infrastructure.
Automation.
Infrastructure automation tasks often rely on resource or service specific tags to indicate whether to opt a resource in or out of an automation.
Access Control.
Some access management policies support tag based conditions. User or role based permissions can use tags to limit or permit access specific environments or VPCs
Documentation.
Well tagged infrastructure gives you the flexibility to use automated diagramming applications like Hava to produce diagrams based on tagged subsets of resources hosted in a single cloud account.
Security Risk Management.
Tags can be applied when creating resources to indicate they process sensitive or confidential data and should have special attention from a security perspective.
Just like code, probably one of the most important aspects of tagging is to adhere to a naming convention. Tags like productionversion, ProductionVersion and production_version while intended to refer to the same collection of resources are treated as very different things.
Azure Tags
Azure tags can be added using PowerShell:
or via your Azure portal:
AWS Tags
AWS tags can easily be added by navigating to the desired resource in your AWS console. Each resource has a "Tags" tab where you add/edit/remove tags.
AWS tags can also be added and modified using the AWS CLI
aws ec2 run-instances \
--image-id ami-abc12345 \
--count 1 \
--instance-type t2.micro \
--key-name MyKeyPair \
--subnet-id subnet-6e7f123e \
--tag-specifications 'ResourceType=instance,Tags=[{Key=webserver,Value=production}]' 'ResourceType=volume,Tags=[{Key=cost-center,Value=cc123}]'
GCP Labels
GCP Labels (Tags) can be easily added at the project level using your GCP console by selecting the "Labels" menu item.
Labels at a resource level can be added by opening your manage resources page, selecting the desired resource and opening the labels tab.
Labels can also be added using the gcloud command line tool. ie:
gcloud compute disks update example-disk --add-labels backend=webserver, media=images
or via API ie:
POST https://compute.googleapis.com/compute/v1/projects/myproject/zones/us-central1-f/instances/example-instance/setLabels
{
"labels": {
"environment": "test",
"an-existing-tag": ""
},
"labelFingerprint": "42WmSpB8rSM="
}
Using Tags to create custom Hava diagrams
Once you have well tagged resources you can leverage your tags to create custom diagrams within Hava.
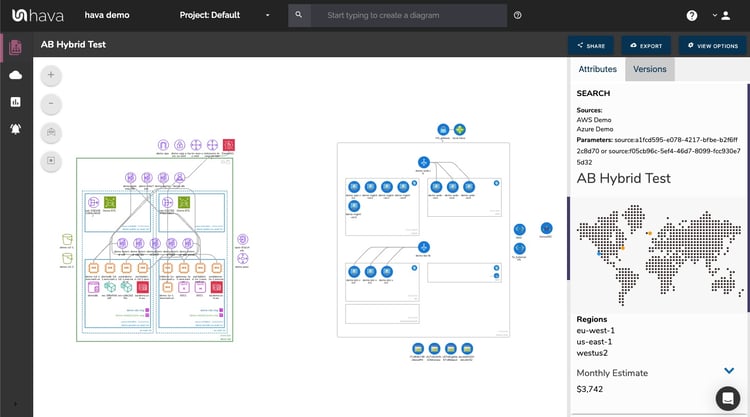
This allows you to achieve things like:
- Segment and document cloud infrastructure by individual tag
- Produce diagrams containing resources just in production
- Produce diagrams for infrastructure in a shared development environment
- Produce diagrams for specific client resources in a managed services environment
- Produce hybrid diagrams from different cloud providers using commonly named tags
- Produce diagrams containing resources of interest to particular roles ie: managing_role: dbAdmin
The options are almost limitless.
Hava provides a query function that will build on-the-fly diagrams based on specified parameters like region:, name:, vpc:, subnet:, virtual_network:, project: and so on.
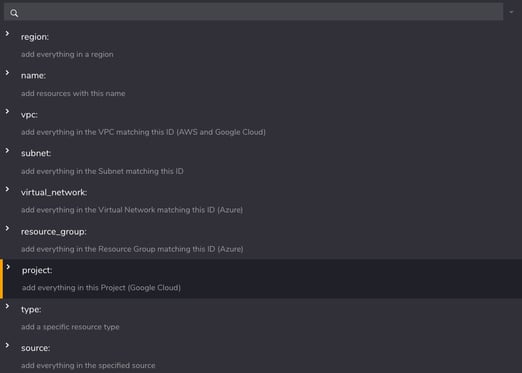
This allows you to build custom diagrams that just include the resources that meet your query. For instance you could enter region:us-east-1 and region:us-east1 to build a diagram that could contain AWS and GCP resources detected in connected cloud accounts.
On top of these pre-defined options is the ability to specify your own custom tag names and the value you wish to match.
Say for instance you have tagged all your resources with a "status" tag of dev, staging or production and also tagged a "security_level" of high, medium or low.
You could produce a diagram for your security team with just "production" resources with a security status of "high" with the following query:
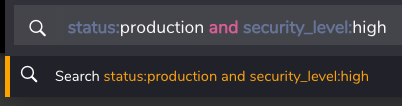
Both the "status" and "security_level" tags are user generated within your AWS, GCP or Azure accounts.
Any query term that is entered into the custom query diagram builder that is not a reserved term in the drop down menu will be treated as a user generated tag/label and the query search will inspect all your resources looking for a match.
Deep Search using Tags
When you create a custom diagram using the style of query above, then only the resources with the nominated tags will be visualised.
Sometimes you need to know what is connected to your tagged resources. To do this, adding the deep search @ prefix will force the diagram to visualise anything connected to your tagged resources.
Excluding Tags
Just as you can specify tags to search and diagram, you can also exclude tags by adding a "-" prefix. -status:production would return everything that is not tagged "production"
This is a useful method when retro tagging your infrastructure to find any un-tagged resources.
If you are currently using Hava to automate your cloud infrastructure then please check out the custom diagram builder utilising tags. If you are not using Hava yet, you can try it out for free for 14 days using the button below.

You can auto generate diagrams, build custom diagrams for Azure, Google Cloud and AWS and compare architecture versions easily - Learn more here