Networking is at the core of just about everything in the cloud. Some elements of your compute infrastructure need to be publicly accessible, while others like databases or transactional applications are better off remaining private.
The way AWS approaches networking is to isolate networks into virtual private clouds (VPCs) which contain subnets with allocated IP address ranges that you set to either private or public.
Public subnets are typically accessible from the internet and are the ingress point for users to access your applications. Public subnets are also typically linked to resources in private subnets that are not publicly visible but are required for applications to function.
Connectivity to AWS
A VPC is a logically isolated segment of the AWS cloud that you define. Within the VPC you define public subnets that may contain resources like a website.
Public VPC Access
To allow public internet traffic into a VPC you need to provision an internet gateway. This routes traffic into your VPC.

A common practice would be to connect the Internet Gateway to an Elastic Load Balancer that would then evenly distribute traffic to EC2 instances in subnets hosted in different availability zones.
Private VPC Access
You may however want to restrict access to private known networks instead of the public internet, in which case you would set up a virtual private gateway that would restrict access to known network traffic only.

This is a VPN connection from your data center or corporate network to your AWS VPC.
AWS Direct Connect
With both public and private methods of accessing your cloud resources mentioned above, the connection is made over public infrastructure. Even the secure and encrypted private VPC access travels over public infrastructure which is subject to latency crushing network congestion unrelated to your network or applications.
To solve this problem, AWS provide AWS Direct Connect.

This is a physical fibre optic connection from your premises to AWS and can be provisioned by an AWS communications partner near you. Direct connect can address the security requirements of high level regulatory and compliance mandates given the connection between your infrastructure and AWS is a physical dedicated connection.
You can have multiple combinations of the above connectivity options on a single VPC, with each connection method connecting to different subnets in the same VPC.
Subnets and Access Control Lists
Your VPC can be considered the outer wall of your virtual network. The gateway lets public or private traffic inside the city walls, but you still get to define which subnets within the VPC that they can access via security settings and IP blocks.
There are two active layers of security checking inter and intra subnet traffic packets. A network access control list is a stateless security function at the subnet level. The ACL will check if traffic trying to enter the subnet is permitted or specifically disallowed. Say for example you have two EC2 instances in separate subnets that need to communicate, the ACL will check eligibility of traffic packets both trying to enter or exit a subnet..
The individual resources like EC2 instances have their own security group. The SG also checks traffic packets trying to access the EC2 instance. The security groups are stateful, so understand and remember where the traffic packets are coming from. Security groups by default let all traffic exit and will validate that requests are being made using specific ports or protocols. An instance hosting a web server for example may allow https traffic but block all other ports and protocols.
By default a security group will block everything until you enable specific types of traffic.
Global Networking
In terms of users around the world accessing your resource instances on AWS, there are a number of services that help users reach your networks.
Route 53 for example, is an AWS DNS service that translates website domain names into the destination server IP address of the desired web property. You can register and buy domain names through Route53 or bring your own. You can set up rules in Route 53 to route traffic to different endpoints. You can set up latency based routing to take users to the fastest available endpoint. You could set up Geolocation routing to route traffic from specific countries to language specific endpoints or weighted round robin to evenly distribute traffic.
Another AWS service Amazon Cloudfront is a content delivery network that caches website data in edge locations close to population centers and will serve content to users from the closest location providing lower latency and a better user experience.
To recap
With AWS, networking is now simplified and condensed down to answer the simple question of “who should be allowed to enter and exit your network”. As long as you can answer that question, then you can set up your network on AWS.
We covered the basics of the AWS VPC, the virtual private cloud and how you use them to isolate your workload in AWS, the fundamentals of network security, including the various gateways, network ACLs, and security groups.
These are all methods that allow your security engineers to build a network that allows healthy traffic access while blocking illegitimate traffic before it reaches your EC2 instances.
We also looked at ways to connect to AWS through VPN and even Direct Connect, secure pipelines that are either encrypted over the general internet or exclusive fiber optics that is used by you exclusively.
We also looked at the global networks that AWS provides using Edge locations, how you can use Route 53 for DNS, and how to use AWS CloudFront to cache content physically closer to your actual users.
So while this only scratches the surface of the many things you can do with AWS networking, in terms of Cloud Practitioner Essentials you should have a better understanding of how AWS networking functions.

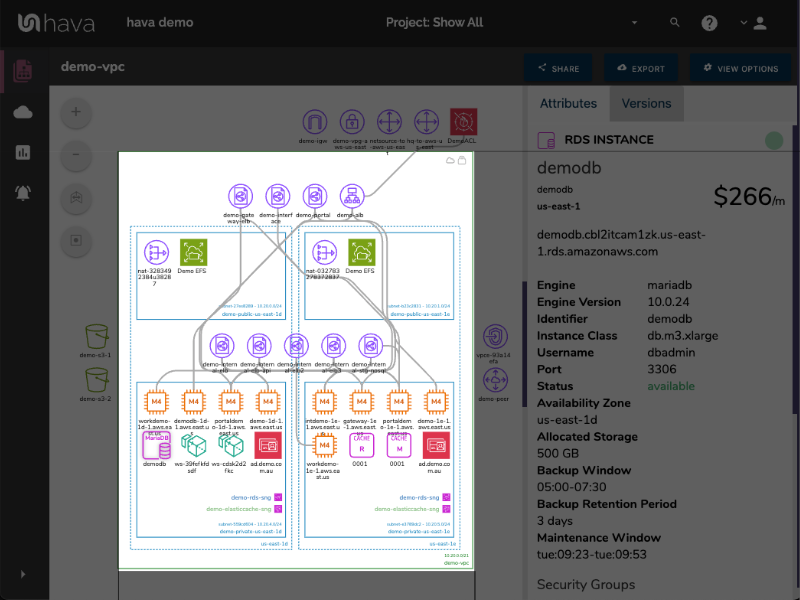
If you are currently not leveraging hava.io to automate the generation and continuous updating of your AWS environment, network topology and security group diagrams, you can take the fully featured Hava Teams plan for a 14 day free trial using the button below.