Classless Inter Domain Routing or CIDR is a prefix based standard for the representation of IP addresses and their routing properties. It was introduced to enable blocks of IP addresses to be grouped together for inclusion in router routing tables instead of needing to include massive blocks of individual IP information.
When you want to get the most out of AWS Security groups or Access Control lists, you should have a good understanding of IPV4 ip address structure and how CIDR Notation is used to describe blocks of IP addresses that you wish to grant access to resources within your cloud infrastructure.
CIDR (Classless Inter-Domain Routing) sometimes referred to as super-netting, is an alternate method of representing a subnet mask and is made up of the binary representation of the network address followed by a slash and a suffix that declares the total number of bits reserved that need to be matched in the address.
To understand the relevance of the trailing suffix value we first need to understand how the decimal IP address we are all used to seeing is viewed by the machines.
192.168.0.0
The IPV4 address 192.168.0.0 under the hood, is broken down into four groups of 8 binary bits each:
11000000.10101000.00000000.00000000
This 32 bit notation is sometimes referred to as a dotted quad. Understanding the 32 bit positions in the IP address, makes the CIDR suffix like 192.168.0.0/16 make more sense. The CIDR trailing suffixes you will typically see are /8 /16 /24 /32 which reference the 8 bit blocks that make up the IP address
When you are defining the range of IP addresses that will be granted access into your network via a security group or an ACL, you tell the configuration how many individual bits of the IP address are a mandatory match, and how many are wild-carded and can be any value.
Using 0 as a value in your IP address configuration implies the value in that 8 bit block of the ip address can be anything.
Let’s say we have a database located at 10.10.50.1 or
00001010.00001010.00110010.00000001
We can use the trailing CIDR notation to define how many of the binary 8 bit blocks should be considered mandatory to allow access.
10.10.0.0/16
The “/16” CIDR notation defines that the first 16 binary values are locked in as mandatory values that must match with the remaining 2 IPv4 ip address octets being wild-carded.
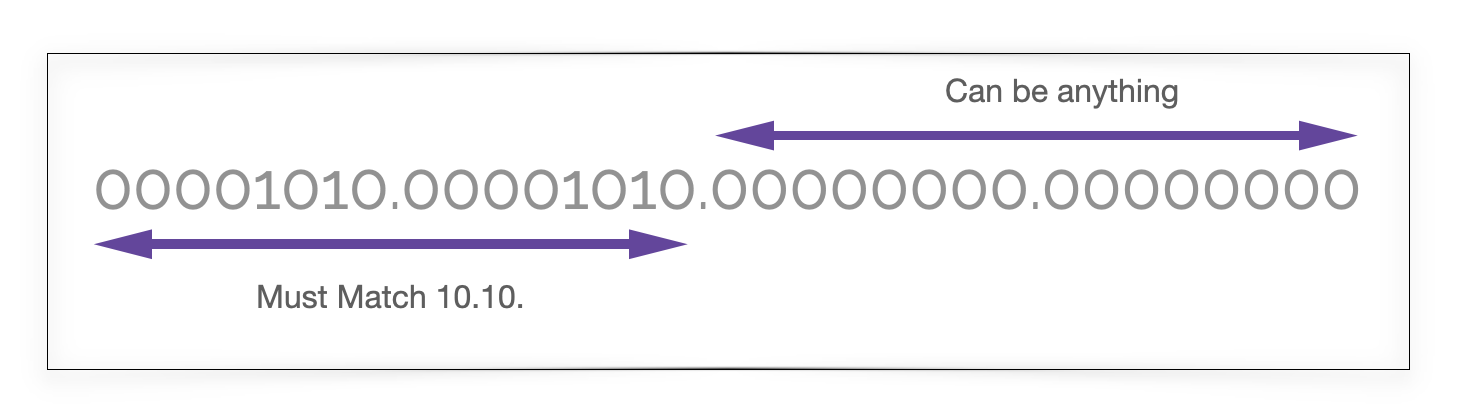
In this scenario any IP address starting with 10.10 gets access to the resource because the first 16 binary bits match.
/16 is probably the most common CIDR suffix used in defining VPC access and gives you around 65 thousand possible IP addresses starting with 10.10.
If you were to use /24 as the CIDR suffix, then only the 4th 8 bit block becomes a variable wildcard giving you the 255 ip addresses 10.10.0.1 through to 10.10.0.255
How to segment subnets using CIDR
You can increase the value of the CIDR suffix to control access to specific subnets and resources.
We could for instance use CIDR notation 10.10.101.0/24 which would allow ip addresses 10.10.101.1 thru 10.10.101.255 access.
The /24 denotes the first 24 binary characters be a fixed match.
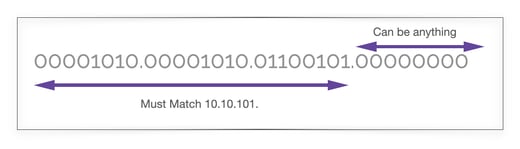 Or - 10.10.101.Anything
Or - 10.10.101.Anything
By the same token you could use /32 to limit access to a single IP address
Ie 10.10.101.1/32 would restrict access to that single IP address.
To allow access from anyone anywhere, like say the internet, you can use 0.0.0.0/0
From time to time you may need or encounter other values in the CIDR notation suffix. For example this IPv4 block:
201.51.100.0/22
This would allow access for the 1024 IPv4 IP addresses from 201.51.100.0 thru to 201.51.103.255
The higher the CIDR suffix, the narrower the number of available IP addresses becomes.
201.51.100.0/23
for instance would allow 512 IP addresses from 201.51.100.0 thru 201.51.101.255
How does CIDR work.
In terms of public IP addresses, Internationally blocks of public IP addresses are handled by the IANA (Internet Assigned Numbers Authority) who are responsible for distributing large blocks of IP addresses to regional internet registries. These blocks are used for large geographical areas like Europe, North America and Africa for example.
From there, subsets of those Ip addresses are typically handled by ISPs who allocate individual public IP addresses to accounts on a fixed IP or shared dynamic basis.
Hardware routers or virtual network gateways use a destination address to route packets to. In terms of cloud computing, this routed traffic will pass through an Access Control List and need to meet security group requirements typically using a CIDR IP address range to restrict access to only traffic that is authorized to communicate with the resources being requested.
CIDR is the routing system used on the internet backbone, the principle data routes between major interconnected networks which forms the core of the internet. Every ISP uses it and CIDR is support by the Border Gateway Protocol (BGP) and the Open Shortest Path First (OSPF) gateway protocol.
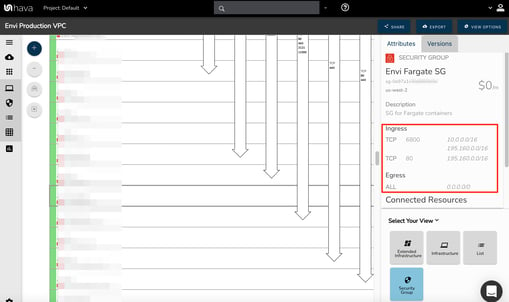
So that's a brief look at CIDR notation and the significance of the trailing slash values you will encounter when viewing security group and ACL configuration metadata in your cloud consoles or when viewing the attribute pane in Hava diagrams :
If you are currently building or supporting applications on AWS, GCP or Microsoft Azure and are not automating your network topology diagrams, then you are welcome to take a free trial using the button below.

If you would like a one-on-one demo and walkthrough of Hava to see if the application suits your use case, then please get in touch.