If your application integrates or handles credit card processing, it's a good idea to ensure your network meets PCI DSS standards.
The Payment Card Industry Data Security Standard is a proprietary information security standard administered by the PCI Security Standards Council which is an organisation founded by American Express, Visa, Mastercard, Discover and JCB International. The standards outlines by the PCI DSS should be adopted by anyone that stores, processes or transmits card holder data or authentication data which would typically be merchants, processors, acquirers, issuers and payment service providers.
If you are handling transactions where the major credit card providers are in use, then they will expect you to be PCI compliant.
Hosting your application on AWS is a good head-start given that AWS is certified as PCI DSS Level 1 service provider. AWS PCi Compliant services include:
-
| SERVICES / PROGRAMS |
SDKs |
PCI |
| Amazon API Gateway |
apigateway |
✓ |
| Amazon AppFlow |
appflow |
✓ |
| Amazon AppStream 2.0 |
appstream |
✓ |
| Amazon Athena |
athena |
✓ |
| Amazon Augmented AI [excludes Public Workforce and Vendor Workforce for all features] |
sagemaker |
✓ |
| Amazon Chime |
chime |
✓ |
Amazon Cloud Directory
|
clouddirectory |
✓ |
| Amazon CloudFront |
cloudfront |
✓ |
| Amazon CloudWatch |
cloudwatch |
✓ |
| Amazon CloudWatch Events [includes Amazon EventBridge] |
events |
✓ |
| Amazon CloudWatch Logs |
logs |
✓ |
| Amazon CloudWatch SDK Metrics for Enterprise Support |
sdkmetrics |
✓ |
| Amazon Cognito |
cognito-idp, cognito-identity, cognito-sync |
✓ |
| Amazon Comprehend |
comprehend |
✓ |
| Amazon Comprehend Medical |
comprehendmedical |
✓ |
| Amazon Connect [excludes Wisdom, VoiceID and High-Volume Outbound Communications] |
connect, connectparticipant |
✓ |
| Amazon Detective |
detective |
✓ |
| Amazon DocumentDB (with MongoDB compatibility) |
|
✓ |
| Amazon DynamoDB |
dynamodb |
✓ |
| Amazon EC2 Auto Scaling |
autoscaling |
✓ |
| Amazon ElastiCache for Redis |
elasticache |
✓ |
| Amazon Elastic Block Store (EBS) |
ec2 |
✓ |
| Amazon Elastic Compute Cloud (EC2) |
ec2 |
✓ |
Amazon Elastic Container Registry (ECR)
|
ecr |
✓ |
| Amazon Elastic Container Service (ECS) [both Fargate and EC2 launch types] |
ecs |
✓ |
| Amazon Elastic File System (EFS) |
elasticfilesystem |
✓ |
| Amazon Elastic Kubernetes Service (EKS) |
eks |
✓ |
| Amazon Elastic MapReduce |
elasticmapreduce |
✓ |
| Amazon FinSpace |
finspace |
✓ |
| Amazon Forecast |
amazonforecast |
✓ |
| Amazon FreeRTOS |
freertos |
✓ |
| Amazon Fraud Detector |
frauddetector |
✓ |
| Amazon FSx |
fsx |
✓ |
| Amazon GuardDuty |
guardduty |
✓ |
| Amazon Inspector |
inspector |
✓ |
| Amazon Kinesis Data Analytics |
kinesisanalytics |
✓ |
| Amazon Kendra |
kendra |
✓ |
| Amazon Keyspaces (for Apache Cassandra) |
keyspaces |
✓ |
| Amazon Kinesis Data Firehose |
firehose |
✓ |
| Amazon Kinesis Data Streams |
kinesis |
✓ |
| Amazon Kinesis Video Streams |
kinesisvideo |
✓ |
| Amazon Lex |
lex |
✓ |
| Amazon Macie |
macie2 |
✓ |
| Amazon Macie Classic |
macie |
✓ |
| Amazon Managed Streaming for Apache Kafka |
kafka |
✓ |
| Amazon MQ |
mq |
✓ |
| Amazon Neptune |
neptune-db |
✓ |
| Amazon OpenSearch Service [successor to Amazon Elasticsearch service] |
elasticsearchservice |
✓ |
| Amazon Personalize |
personalize |
✓ |
| Amazon Pinpoint |
mobiletargeting |
✓ |
| Amazon Polly |
polly |
✓ |
| Amazon Quantum Ledger Database (QLDB) |
qldb |
✓ |
| Amazon Quicksight |
quicksight |
✓ |
| Amazon Redshift |
redshift |
✓ |
| Amazon Rekognition |
rekognition |
✓ |
| Amazon Relational Database Service (RDS) [includes Amazon Aurora] |
rds |
✓ |
| Amazon Route 53 |
route53 |
✓ |
| Amazon S3 Glacier |
glacier |
✓ |
| Amazon S3 Transfer Acceleration |
s3transferacceleration |
✓ |
Amazon SageMaker [excludes Studio Lab, Ground Truth Plus, Public Workforce and Vendor Workforce for all features]
|
sagemaker |
✓ |
| Amazon SimpleDB |
sbd |
✓ |
| Amazon Simple Email Service |
ses |
✓ |
| Amazon Simple Notification Service (SNS) |
sns |
✓ |
| Amazon Simple Queue Service (SQS) |
sqs |
✓ |
| Amazon Simple Storage Service (S3) |
s3 |
✓ |
| Amazon Simple Workflow Service (SWF) |
swf |
✓ |
| Amazon Textract |
textract |
✓ |
| Amazon Timestream |
timestreamquery, timestreamwrite |
✓ |
| Amazon Transcribe |
transcribe |
✓ |
| Amazon Translate |
translate |
✓ |
| Amazon Virtual Private Cloud (VPC) |
ec2 |
✓ |
| Amazon WorkDocs |
workdocs |
✓ |
| Amazon WorkLink |
worklink |
✓ |
| Amazon WorkSpaces |
workspaces |
✓ |
| AWS Amplify [includes AWS Amplify Console] |
amplify |
✓ |
| AWS Application Migration Service |
mgn |
✓ |
| AWS App Mesh |
appmesh |
✓ |
| AWS App Runner |
apprunner |
✓ |
| AWS AppSync |
appsync |
✓ |
| AWS Audit Manager |
auditmanager |
✓ |
| AWS Backup |
backup |
✓ |
| AWS Batch |
batch |
✓ |
| AWS Certificate Manager (ACM) |
acm |
✓ |
| AWS Chatbot |
|
✓ |
| AWS Cloud Map |
servicediscovery |
✓ |
| AWS Cloud9 |
cloud9 |
✓ |
| AWS CloudFormation |
cloudformation |
✓ |
| AWS CloudHSM |
cloudhsm |
✓ |
| AWS CloudTrail |
cloudtrail |
✓ |
| AWS CodeBuild |
codebuild |
✓ |
| AWS CodeCommit |
codecommit |
✓ |
| AWS CodeDeploy |
codedeploy |
✓ |
| AWS CodePipeline |
codepipeline |
✓ |
| AWS Control Tower |
controltower |
✓ |
| AWS Config |
config |
✓ |
| AWS Database Migration Service |
dms |
✓ |
| AWS DataSync |
datasync |
✓ |
| AWS Data Exchange |
dataexchange |
✓ |
| AWS Direct Connect |
directconnect |
✓ |
| AWS Directory Service [excludes Simple AD] |
ds |
✓ |
| AWS Elastic Beanstalk |
elasticbeanstalk |
✓ |
| AWS Elemental MediaConnect |
mediaconnect |
✓ |
| AWS Elemental MediaConvert |
mediaconvert |
✓ |
| AWS Elemental MediaLive |
medialive |
✓ |
| AWS Firewall Manager |
fms |
✓ |
| AWS Global Accelerator |
globalaccelerator |
✓ |
| AWS Glue [includes AWS Lake Formation] |
glue |
✓ |
| AWS Glue DataBrew |
databrew |
✓ |
| AWS Ground Station |
groundstation |
✓ |
| AWS Identity & Access Management (IAM) |
iam |
✓ |
| AWS IoT Core |
iot |
✓ |
| AWS IoT Device Management |
iot |
✓ |
| AWS IoT Events |
iotcolumbodata, iotcolumbo |
✓ |
| AWS IoT Greengrass |
greengrass |
✓ |
| AWS Key Management Service |
kms |
✓ |
| AWS Lambda |
lambda |
✓ |
| AWS Lambda@Edge |
lambdaedge |
✓ |
| AWS License Manager |
license-manager |
✓ |
| AWS Managed Services |
|
✓ |
| AWS Network Firewall |
network-firewall |
✓ |
| AWS OpsWorks CM [includes Chef Automate, Puppet Enterprise] |
opsworks-cm |
✓ |
| AWS OpsWorks Stacks |
opsworks |
✓ |
| AWS Organizations |
organizations |
✓ |
| AWS Outposts |
outposts |
✓ |
| AWS Personal Health Dashboard |
health |
✓ |
| AWS Private Certificate Authority |
ACMPrivateCA |
✓ |
| AWS Resource Access Manager |
ram |
✓ |
| AWS Resource Groups |
resource-groups |
✓ |
| AWS RoboMaker |
robomaker |
✓ |
| AWS Secrets Manager |
secretsmanager |
✓ |
| AWS Security Hub |
securityhub |
✓ |
| AWS Server Migration Service (SMS) |
sms |
✓ |
| AWS Serverless Application Repository |
serverlessrepo |
✓ |
| AWS Service Catalog |
servicecatalog |
✓ |
| AWS Single Sign-On |
sso |
✓ |
| AWS Shield |
shield, DDoSProtection |
✓ |
| AWS Snowball |
snowball |
✓ |
| AWS Snowball Edge |
snowballedge |
✓ |
| AWS Snowmobile |
snowmobile |
✓ |
| AWS Step Functions |
states |
✓ |
| AWS Storage Gateway |
storagegateway |
✓ |
| AWS Systems Manager |
ssm |
✓ |
| AWS Transfer for SFTP |
transfer |
✓ |
| AWS Trusted Advisor |
trustedadvisor |
✓ |
| AWS WAF |
waf |
✓ |
| AWS X-Ray |
xray |
✓ |
| EC2 Image Builder |
imagebuilder |
✓ |
| Elastic Load Balancing |
elasticloadbalancing |
✓ |
| VM Import/Export |
|
✓ |
You still need to make sure you have PCI DSS requirements covered which include:
- Install and maintain a firewall in front of cardholder data
- Change vendor provided default security and system passwords
- Encrypt cardholder data in transit and at rest
- Protect against malware and keep anti-virus software up to date
- Develop secure systems
- Restrict data access to cardholder information internally
- Restrict and authenticate access to key system components
- Track and monitor access to your network
So as a customer who uses AWS to store, process or transmit cardholder data you have a solid base as you manage your own PCI DSS compliance.
AWS however does not automatically have everything covered. The shared responsibility model you enter into when using AWS services means they provide the mechanisms to perform forensic investigations when things go wrong, but it is ultimately your responsibility to prove your systems are up to scratch.
That's where an AWS PCI diagrams comes into play. Or more specifically the diagrams auto-generated by Hava.
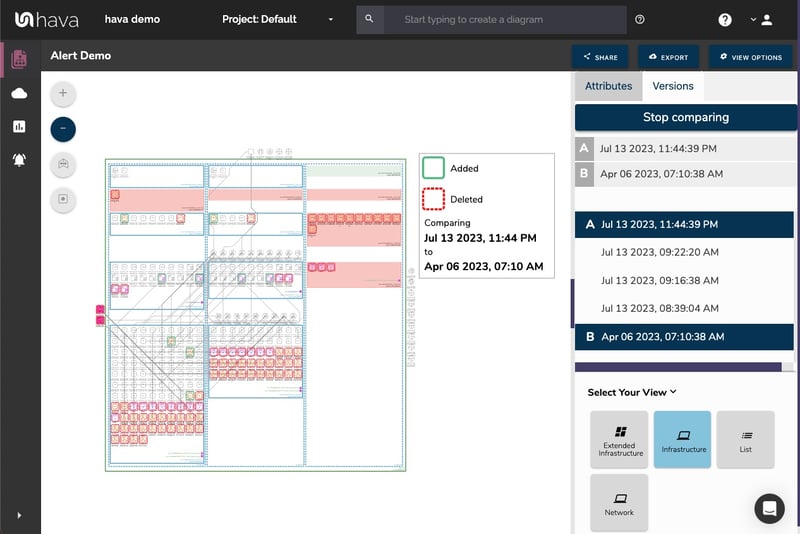
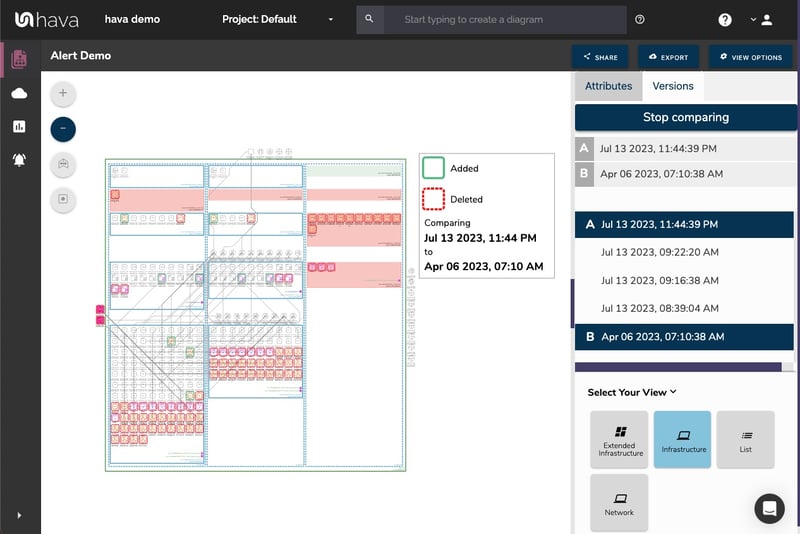
Because the network topology diagrams created by Hava are auto generated and cannot be edited (without exporting diagrams out of the platform) they can be relied on as a source of truth. The diagrams reflect exactly what is running now, and probably more usefully show what was running at any point in time when you investigate the diagrams stored in version history.
As changes are detected in your AWS configuration, Hava generates a new diagram set and places the superseded diagrams into version history. The historical diagrams are fully interactive, so you can investigate all the metadata related to anything on the diagram.
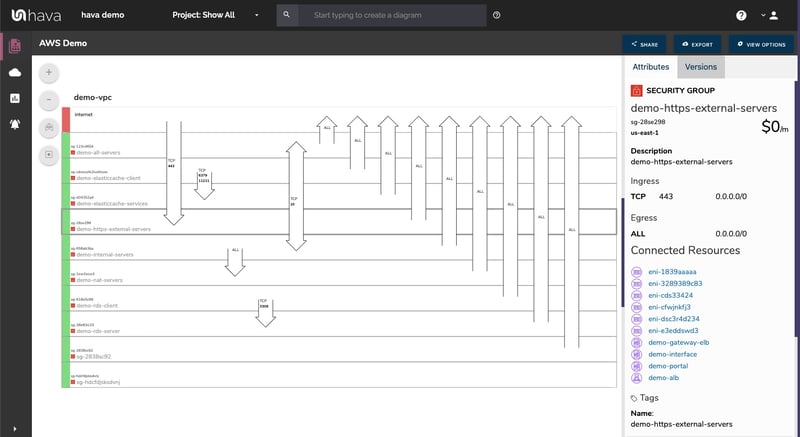
As well as proving the existence of key security components like firewalls and data encryption, Hava provides other key security detail on the security view diagram:
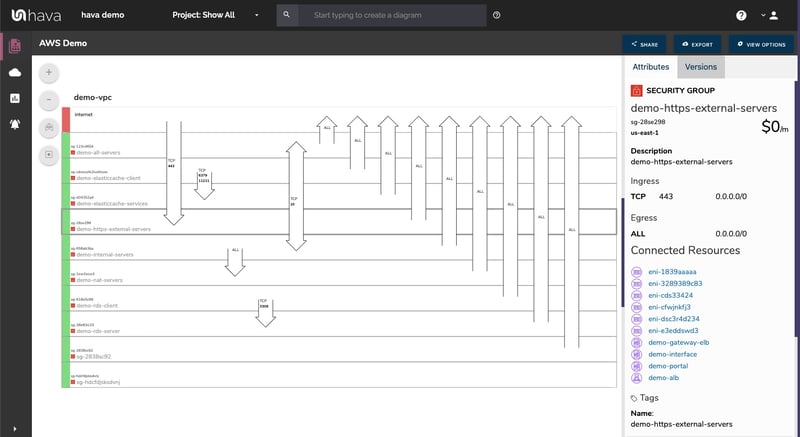
The security view shows you all of your security groups and overlays the configured ports and the points at which they enter and exit your cloud infrastructure. This helps with your PCI compliance by showing that all your traffic is encrypted and securely managed.
The security view is also stored in version history when changes are detected, so can also be accessed for audit purposes.
If you are building or supporting applications on AWS, Azure or GCP you can check out what your environments look like in diagram form by taking Hava for a 14 day free trial using the button below.